Building a Virtual Security Home Lab: Part 5 - Cyber Range Setup
A step-by-step guide for building your very own Cybersecurity Home Lab using VirtualBox
A step-by-step guide for building your very own Cybersecurity Home Lab using VirtualBox
A step-by-step guide for building your very own Cybersecurity Home Lab using VirtualBox

A step-by-step guide for building your very own Cybersecurity Home Lab using VirtualBox
A step-by-step guide for building your very own Cybersecurity Home Lab using VirtualBox
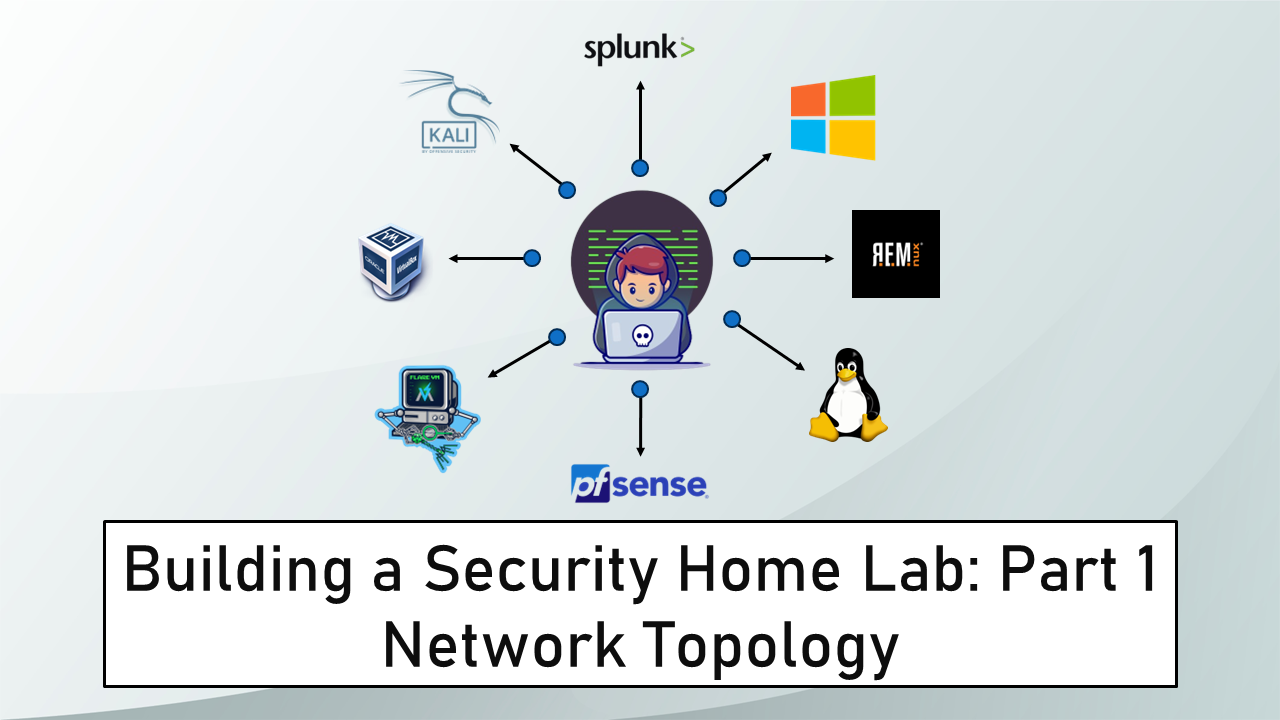
A step-by-step guide for building your very own Cybersecurity Home Lab using VirtualBox
Get started with Cyber Security in 24 Days - Learn the basics by doing a new, beginner-friendly security challenge every day leading up to Christmas.
Get started with Cyber Security in 24 Days - Learn the basics by doing a new, beginner-friendly security challenge every day leading up to Christmas.
Get started with Cyber Security in 24 Days - Learn the basics by doing a new, beginner-friendly security challenge every day leading up to Christmas.
Get started with Cyber Security in 24 Days - Learn the basics by doing a new, beginner-friendly security challenge every day leading up to Christmas.
Get started with Cyber Security in 24 Days - Learn the basics by doing a new, beginner-friendly security challenge every day leading up to Christmas.
Get started with Cyber Security in 24 Days - Learn the basics by doing a new, beginner-friendly security challenge every day leading up to Christmas.
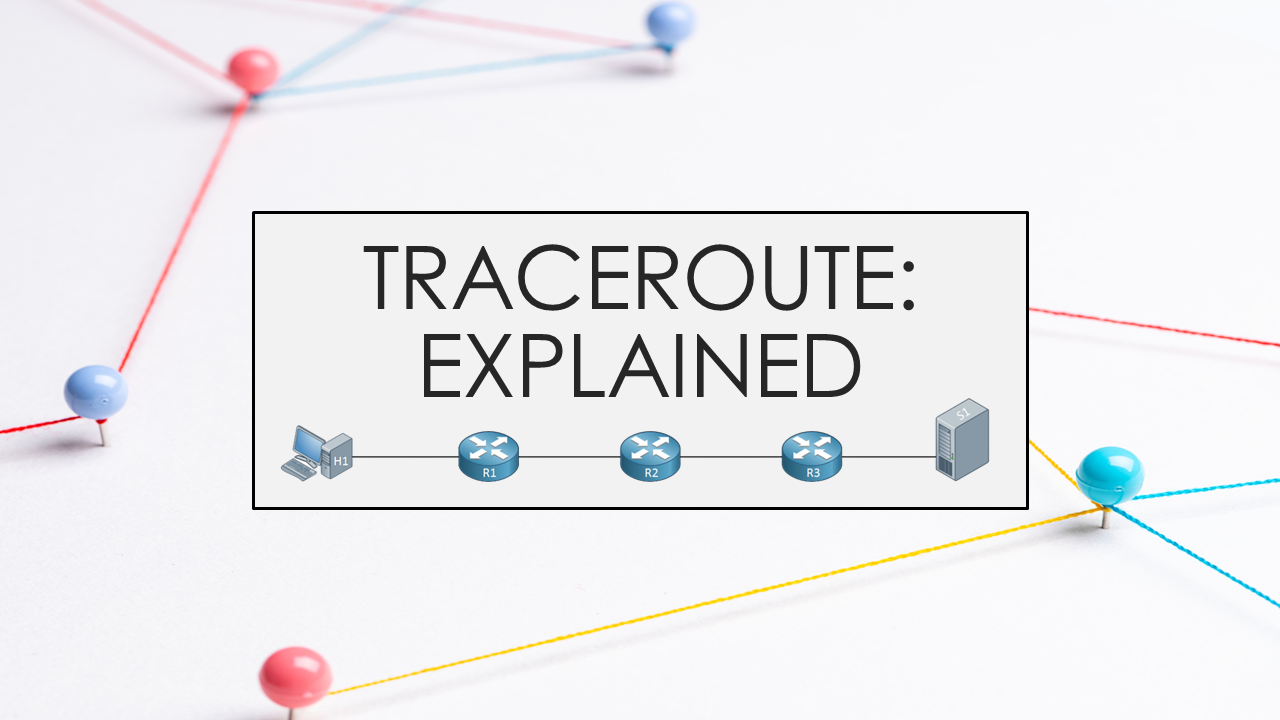
The what, why and how of the network debugging tool traceroute
Create executables from Python code easily using a simple and intuitive GUI

Apply learned skills to probe malicious emails and URLs, exposing a vast phishing campaign

You found a secret server located under the deep sea. Your task is to hack inside the server and reveal the truth